Robert Hanssen: Double agent
17 results back to index

pages: 299 words: 88,375
Gray Day: My Undercover Mission to Expose America's First Cyber Spy by Eric O'Neill
active measures, autonomous vehicles, Berlin Wall, bitcoin, computer age, cryptocurrency, deep learning, disinformation, Dissolution of the Soviet Union, Edward Snowden, Fall of the Berlin Wall, false flag, fear of failure, full text search, index card, information security, Internet of things, Kickstarter, messenger bag, Mikhail Gorbachev, operational security, PalmPilot, ransomware, rent control, Robert Hanssen: Double agent, Ronald Reagan, Skype, thinkpad, Timothy McVeigh, web application, white picket fence, WikiLeaks, young professional
In June 1997, after pleading guilty to conspiracy to commit espionage, Earl Pitts was sentenced to twenty-seven years in prison. I had long since left Donner’s squad to finally attend the FBI Academy at Quantico, so I wasn’t around for Pitts’s lengthy debrief, when he mentioned that another FBI agent made him suspicious. Pitts suspected that agent might also be a spy. At the time, the FBI dismissed Pitts’s concerns and chose not to follow up with the agent he’d named: an obscure computer expert named Robert Hanssen. CHAPTER 3 LAY DOWN YOUR SWORD Gene’s blue Crown Victoria prowled away toward Pennsylvania Avenue and FBI headquarters. I watched him turn the corner and then stood for a few minutes in the cold.
…
He was also weeks away from a drop that might end in his arrest or, if we missed it, a last payout before he took his retirement and we lost our chance. So much hinged on what I learned in 9930. But while the agents in the secret squad room had piles of evidence, I had nothing. No information, no leads, no case. Target: Robert Hanssen Russian mole Gray Suit, potentially Ramon Garcia, B Shared nuclear secrets Compromised overseas assets Worst spy in American history CHAPTER 18 MAKING A SPY In January 1976, Robert Hanssen joined the FBI. His credentials as a certified public accountant with a master’s degree in business administration complemented four years spent on the Chicago police force to make him a good fit for the agency’s Financial Crimes Division, and he was assigned to Gary, Indiana, right out of the FBI Academy.
…
This was one reason I was tapped over a more seasoned agent: I was the most out-of-sight, unexpected person the FBI could find. When Gene parked in front of my apartment that frigid December morning, he’d asked me if I’d ever heard of Robert Hanssen. But that wasn’t what he was really asking. His real question was underneath that question: Had Hanssen ever heard of me? If Hanssen wasn’t on my radar, I likely wasn’t on his—or anyone else’s, for that matter. Which is why no one, not even Hanssen, would suspect me. An analyst pulled me out of my epiphany: “He’s on his way back.” Kate led me past the desks of agents that reminded me of the small team assembled to catch Earl Pitts.

Spies, Lies, and Algorithms by Amy B. Zegart
2021 United States Capitol attack, 4chan, active measures, air gap, airport security, Apollo 13, Bellingcat, Bernie Sanders, Bletchley Park, Chelsea Manning, classic study, cloud computing, cognitive bias, commoditize, coronavirus, correlation does not imply causation, COVID-19, crowdsourcing, cryptocurrency, cuban missile crisis, Daniel Kahneman / Amos Tversky, deep learning, deepfake, DeepMind, disinformation, Donald Trump, drone strike, dual-use technology, Edward Snowden, Elon Musk, en.wikipedia.org, end-to-end encryption, failed state, feminist movement, framing effect, fundamental attribution error, Gene Kranz, global pandemic, global supply chain, Google Earth, index card, information asymmetry, information security, Internet of things, job automation, John Markoff, lockdown, Lyft, Mark Zuckerberg, Nate Silver, Network effects, off-the-grid, openstreetmap, operational security, Parler "social media", post-truth, power law, principal–agent problem, QAnon, RAND corporation, Richard Feynman, risk tolerance, Robert Hanssen: Double agent, Ronald Reagan, Rubik’s Cube, Russian election interference, Saturday Night Live, selection bias, seminal paper, Seymour Hersh, Silicon Valley, Steve Jobs, Stuxnet, synthetic biology, uber lyft, unit 8200, uranium enrichment, WikiLeaks, zero day, zero-sum game
Olson insisted his teams have at least a year in the city of operation before he would allow them to start surveillance operations there. A single twenty-four-hour FBI surveillance operation of one terrorist suspect or foreign intelligence officer takes more than two dozen people.45 The best way to uncover traitors at home is by penetrating hostile intelligence services abroad. As counterintelligence officials have noted, it takes a mole to catch a mole.46 That’s how the FBI ultimately caught Robert Hanssen. For years before Hanssen’s 2001 arrest, the FBI and CIA knew that someone in the U.S. government was handing over vital secrets to the Russians. They worked furiously to find the mole, without success, spending three years chasing the wrong man, a CIA officer named Brian Kelley.
…
Johanna McGeary, “The FBI spy it took 15 years to discover,” Time, March 5, 2001, http://content.time.com/time/world/article/0,8599,2047748,00.html. 6. James Olson, To Catch a Spy: The Art of Counterintelligence (Washington D.C.: Georgetown University Press, 2019), xiii; Masters, “Hanssen Admits Spying, Avoids Death Penalty”; Eric Lichtblau, “Report Details FBI’s Security Failings and Missed Spy Signals,” Los Angeles Times, April 5, 2002, https://www.latimes.com/archives/la-xpm-2002-apr-05-mn-36370-story.html (accessed August 22, 2020). 7. Federal Bureau of Investigation, “Robert Hanssen,” History, https://www.fbi.gov/history/famous-cases/robert-hanssen (accessed August 23, 2020). 8.
…
Trying not to fool ourselves is a worthy endeavor, and evidence suggests it is likely to get better as we learn more about the processes and practices that make some individuals and groups more accurate than others and as new technologies enhance the quest for insight. 6 COUNTERINTELLIGENCE TO CATCH A SPY Never go home at night without wondering where the mole is. —ROBERT GATES, CIA DIRECTOR, 1991–19931 ROBERT HANSSEN SEEMED an unlikely traitor. The son of a Chicago police officer, he majored in chemistry and went to graduate school in dentistry before getting his MBA from Northwestern University. In 1976, after stints as an accountant and a police officer, Hanssen joined the FBI, where he worked for the next twenty-five years.2 Colleagues found him socially awkward but smart, with a strong interest in computers. Hanssen was a devoted husband, a father of six children, and a devout Catholic who went to Mass almost every day.

pages: 291 words: 85,908
The Skripal Files by Mark Urban
Berlin Wall, Boris Johnson, disinformation, Donald Trump, drone strike, fake news, Fall of the Berlin Wall, false flag, Jeremy Corbyn, Mikhail Gorbachev, military-industrial complex, moral hazard, Robert Hanssen: Double agent, Skype
Soon after Bush’s inauguration in January 2001, the FBI mole Robert Hanssen was arrested, and it emerged what extraordinary damage he’d done to US intelligence operations during years of spying. President Bush expelled fifty Russian diplomats, six of whom had been directly involved in running Hanssen, as a way of showing his displeasure. This readiness to be much firmer in the face of Moscow’s spying operations was to prove short-lived, though. 9/11 imposed new imperatives. Keeping supply lines to Afghanistan open meant American diplomats wanted to look the other way when it came to SVR or GRU activity. For the American or British agent networks in Russia, however, the risks remained the same, even if the bureaucrats in Washington or London were less interested in the product.
…
In the meantime Florez busied himself with a number of projects, including a paper on techniques for recruiting human sources. Being back at headquarters, Florez was able to access and copy all manner of secret documents. Given the study he was engaged in, he would have been well aware of the activities of one of Russia’s most successful penetrations ever, FBI agent Robert Hanssen, since he was arrested early in 2001. Hanssen’s long spying career, going back to the mid-1980s, depended for most of its length on never meeting the Russians face to face. The Russians were too heavily penetrated for him to want to do it any other way. Hanssen provided classified information (leading to the death of several Russians working for the Americans), and the Russians in return left him large amounts of cash in dead drops.
…
For as Putin had explained to that Russian journalist, enemies you can accommodate or deal with. Traitors must be crushed. Alexander Zaporozhsky was a case in point. He had been an extremely valuable CIA penetration while serving as deputy chief of the SVR’s North America desk. It was rumoured that he might even have been responsible for the exposure of Robert Hanssen. Zaporozhsky had been recruited by the Americans during the free-for-all of the mid-1990s, quitting the SVR a couple of years later, in 1997, before being exfiltrated to the US. Just two months after the 9/11 attacks, the SVR man, who lived near Baltimore, had been chatting over the phone to friends in Russia who suggested that he join them for a big celebration they were planning.
pages: 461 words: 125,845
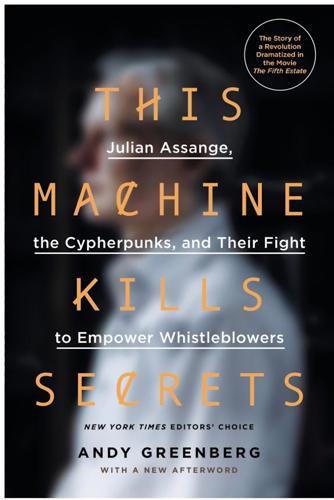
This Machine Kills Secrets: Julian Assange, the Cypherpunks, and Their Fight to Empower Whistleblowers by Andy Greenberg
air gap, Apple II, Ayatollah Khomeini, Berlin Wall, Bill Gates: Altair 8800, Bletchley Park, Burning Man, Chelsea Manning, computerized markets, crowdsourcing, cryptocurrency, disinformation, domain-specific language, driverless car, drone strike, en.wikipedia.org, Evgeny Morozov, Fairchild Semiconductor, fault tolerance, hive mind, information security, Jacob Appelbaum, John Gilmore, John Perry Barlow, Julian Assange, Lewis Mumford, Mahatma Gandhi, military-industrial complex, Mitch Kapor, MITM: man-in-the-middle, Mohammed Bouazizi, Mondo 2000, Neal Stephenson, nuclear winter, offshore financial centre, operational security, PalmPilot, pattern recognition, profit motive, Ralph Nader, real-name policy, reality distortion field, Richard Stallman, Robert Hanssen: Double agent, Silicon Valley, Silicon Valley ideology, Skype, social graph, SQL injection, statistical model, stem cell, Steve Jobs, Steve Wozniak, Steven Levy, Teledyne, three-masted sailing ship, undersea cable, Vernor Vinge, We are Anonymous. We are Legion, We are the 99%, WikiLeaks, X Prize, Zimmermann PGP
And finally comes the leak itself, the moment when the insider walks out of the building with the physical material in hand, pushes it out by e-mail, or spills it onto the Web. Even after the initial leak, Mudge argues, the “tells” might continue. He points to the case of Robert Hanssen, a former FBI agent currently serving a life sentence in a Colorado supermax prison for giving intelligence information to the Soviets over two decades. In 2002, he confessed to selling the USSR $1.4 million in secrets, from signals intelligence methods to the fact that the FBI had dug an eavesdropping tunnel under the Soviet embassy in Washington, D.C. Every few days, Hanssen would stop his normal activities and make a single query to a server across the network, a pattern he repeated for almost ten years.
…
Lamo has responded by closing his eyes and allowing his head to bob and sink slowly for several seconds. I consider reaching over to tap him on the shoulder. Before I do, he suddenly looks up and answers me. “The man is the equivalent of a spy. He’s our next Aldrich Ames or Robert Hanssen,” Lamo says, naming two convicted double agents who sold information to the USSR over several decades. Lamo’s speech is a robotic slur, a result of the cocktail of psychoactive prescription drugs he takes daily. But his hazel eyes have opened wide and he’s now staring at me with surprising lucidity. “The only difference is that instead of giving information to the Soviets, he’s giving it to an antisecrecy organization.
…
If a Paranoia Meter has found its way into DARPA’s budget, reconceived in a form that better suits the agency’s standards, Mudge isn’t telling. For now, the results of his work, like the information it’s meant to protect, have become another sealed file in the Pentagon’s vault of secrets. The individuals tasked with rooting out leaks—from Adrian Lamo to Aaron Barr—tend to compare their targets to Robert Hanssen and Aldrich Ames, spies who sold uncountable secrets to foreign empires for millions of dollars. In fact, the archetypal leaker is often more like one NSA analyst named Thomas Drake: a conscientious whistleblower repaid only with crushing legal retribution. Drake, a thin and severe-looking man with a wisp of brown hair, has the hard stare of someone who has dealt in serious affairs and seen them go very badly.

pages: 400 words: 121,708
1983: Reagan, Andropov, and a World on the Brink by Taylor Downing
Able Archer 83, active measures, anti-communist, Ayatollah Khomeini, Berlin Wall, Boeing 747, cuban missile crisis, disinformation, Donald Trump, Dr. Strangelove, fake news, Fall of the Berlin Wall, full employment, Herman Kahn, Korean Air Lines Flight 007, kremlinology, Mikhail Gorbachev, military-industrial complex, mutually assured destruction, nuclear paranoia, nuclear winter, RAND corporation, Robert Hanssen: Double agent, Ronald Reagan, Ronald Reagan: Tear down this wall, Seymour Hersh, Stanislav Petrov, Strategic Defense Initiative, Vladimir Vetrov: Farewell Dossier, Yom Kippur War
Secondly, they now realised they could trust the evidence Ames was selling to them.5 On the evening of the disastrous failed handover in Moscow, in a restaurant in the smart suburb of Washington DC known as Georgetown, Ames handed to his KGB minder a bag containing probably ‘the largest batch of sensitive documents and critical information ever turned over to the KGB in a single meeting’.6 It included information about at least ten Soviets who were passing top-level intelligence to the CIA, the FBI or other Western agencies, among them Gordievsky and Tolkachev. The KGB now had proof of their activities. Tolkachev was kept in prison and interrogated for a little over a year. The KGB wanted to know exactly how his betrayal had come about and every detail of how he had supplied the Americans with aviation intelligence. He was finally executed for treason in September 1986. In October 1985, Robert Hanssen, an FBI agent of some twelve years’ standing, an analyst on Soviet affairs based in New York, also made contact by letter with the KGB officer in Washington who was running Aldrich Ames, Viktor Cherkashin.
…
New York: Simon & Schuster, 1992. Volkogonov, Dmitri, The Rise and Fall of the Soviet Empire: Political Leaders from Lenin to Gorbachev. London: HarperCollins, 1998. Voslensky, Michael (tr. E. Mosbacher), Nomenklatura. London: The Bodley Head, 1990. Wise, David, Spy: The Inside Story of How the FBI’s Robert Hanssen Betrayed America. New York: Random House, 2002. Zubok, Vladislav, A Failed Empire: The Soviet Union in the Cold War from Stalin to Gorbachev. Chapel Hill: University of North Carolina Press, 2009. Key Sources NSA The National Security Archive is a non-governmental research and archive organisation located at George Washington University, Washington DC.
…
And the bi-polar world of the second half of the twentieth century prepared to transition awkwardly into the multi-polar and arguably even more dangerous world of the twenty-first century. Spies had played a leading role in the events of the tense year of 1983, as we have seen. Despite the end of the Cold War, the spying of Aldrich Ames and Robert Hanssen carried on for some years with both men selling secrets to the Russian Federation. Ames was finally tracked down by an internal CIA inquiry and was arrested in February 1994. He initially declared he was innocent but later admitted his guilt and was given a life sentence without remission. His wife Rosario was given a five-year sentence for tax evasion.

pages: 562 words: 153,825
Dark Mirror: Edward Snowden and the Surveillance State by Barton Gellman
4chan, A Declaration of the Independence of Cyberspace, Aaron Swartz, active measures, air gap, Anton Chekhov, Big Tech, bitcoin, Cass Sunstein, Citizen Lab, cloud computing, corporate governance, crowdsourcing, data acquisition, data science, Debian, desegregation, Donald Trump, Edward Snowden, end-to-end encryption, evil maid attack, financial independence, Firefox, GnuPG, Google Hangouts, housing justice, informal economy, information security, Jacob Appelbaum, job automation, John Perry Barlow, Julian Assange, Ken Thompson, Laura Poitras, MITM: man-in-the-middle, national security letter, off-the-grid, operational security, planetary scale, private military company, ransomware, Reflections on Trusting Trust, Robert Gordon, Robert Hanssen: Double agent, rolodex, Ronald Reagan, Saturday Night Live, seminal paper, Seymour Hersh, Silicon Valley, Skype, social graph, standardized shipping container, Steven Levy, TED Talk, telepresence, the long tail, undersea cable, Wayback Machine, web of trust, WikiLeaks, zero day, Zimmermann PGP
“Snowden claims that he’s won”: James Clapper, testimony before the Senate Select Committee on Intelligence, January 29, 2014, transcribed at http://wapo.st/2b26smO and archived at https://archive.is/QxYVN. The relevant video excerpt is https://youtu.be/CowlDnng2Zc. Snowden’s “agents”: The NSA inspector general compared Snowden and his journalistic “agents” unfavorably to notorious FBI traitor Robert Hanssen, saying “Hanssen’s theft was in a sense finite whereas Snowden is open-ended, as his agents decide daily which documents to disclose.” George Ellard, panel remarks, “A New Paradigm of Leaking,” Symposium on Leakers, Whistleblowers and Traitors, February 25, 2014, transcript available at Journal of National Security Law & Policy 8, no. 1 (2015).
…
This is the whole business about one man’s whistleblower is another man’s spy.” In a similar vein came remarks by the NSA inspector general, George Ellard. Twice in February 2014, both times as I sat within his sight, Ellard referred to journalists on the story as Snowden’s “agents.” We had done more damage, he said at a Georgetown University conference, than the notorious FBI traitor Robert Hanssen, who helped Soviet security services hunt down and kill U.S. intelligence assets. Tight-lipped and curt, he walked away when someone introduced us after the panel. When we finally spoke nearly two years later, he said, “I must confess I read your work with keen interest.”
…
“the rise of political doxing”: Bruce Schneier, “The Rise of Political Doxing,” Vice, October 28, 2015, www.vice.com/en_us/article/z43bm8/the-rise-of-political-doxing. She was a crisis manager: Vanee Vines portrayed herself this way in her LinkedIn profile, www.linkedin.com/in/vaneevines/. to the worst traitor: I wrote about George Ellard’s comment, comparing Snowden and his “agent” journalists to FBI traitor Robert Hanssen, in chapter 7. “It sounds like I won’t”: Snowden chat with author, November 22, 2013. require extraordinary evidence: The aphorism was popularized by astronomer Carl Sagan in his 1980 television show Cosmos. It is a staple in the worlds of science, intelligence, and journalism.

pages: 525 words: 131,496
Near and Distant Neighbors: A New History of Soviet Intelligence by Jonathan Haslam
active measures, Albert Einstein, Benoit Mandelbrot, Berlin Wall, Bletchley Park, Bolshevik threat, Bretton Woods, British Empire, cuban missile crisis, disinformation, falling living standards, false flag, John von Neumann, lateral thinking, military-industrial complex, Robert Hanssen: Double agent, Ronald Reagan, Strategic Defense Initiative, Valery Gerasimov, Vladimir Vetrov: Farewell Dossier, éminence grise
One underlying vulnerability of the Soviet system was loss of faith, a loss initially delayed at home through timely populism, but immediately damaging abroad. In the end it meant that recruitment of agents could be based almost exclusively upon material incentives. It also meant that as time went on and stagnation took hold at home, Soviet citizens and operatives increasingly fell victim to hostile recruitment. The Americans, too, had succumbed to disillusion as a consequence of the failed war in Vietnam, and the Russians took every opportunity to undermine their U.S. counterparts from within: hence the betrayal of CIA by Aldrich Ames and the FBI by Robert Hanssen. Of course none of this availed Moscow, except in the short term, as the Soviet Union’s ultimate collapse was due to forces far larger than secret intelligence could muster or block.
…
Even when Cherkashin identified Valerii Martynov as the culprit, nothing was done until eventually Martynov was named by others.48 U.S. human intelligence operations in the Soviet Union, always a point of vulnerability, collapsed under the successful Soviet counterintelligence drive accelerated by Andropov—at least that is what Major General Rem Krasil’nikov, head of the first (American) department of the KGB’s Second Main Directorate (1979–1992), claims. In fact, the American effort collapsed under the weight of the greed at the heart of its own intelligence establishment. Robert Hanssen at the FBI was responsible for counterintelligence against Soviet operations. From 1979 to 2001, Hanssen gave Moscow the names of those Russians he knew to have been recruited by the American services within the United States. “Perhaps for some in Russia, the 1960s and the beginning of the 1980s were the years of social stagnation,” the former KGB rezident Solomatin recalled with smug satisfaction.
…
Colonel Viktor Cherkashin, head of foreign counterintelligence at the rezidentura, was never consulted on this, and on returning from leave in March 1984 expressed his horror. All it needed was an American agent in their midst, and the FBI could watch for all operatives meeting their contacts to roll up whatever activities were in progress. When Cherkashin tested his hunch by creating a fictitious new operative, only to find the FBI on the ground awaiting him, Androsov refused to acknowledge the implications of this discovery—that there was, indeed, an FBI agent in their midst—since reporting it would jeopardise his own continuation in post and Kryuchkov’s standing, too. Even when Cherkashin identified Valerii Martynov as the culprit, nothing was done until eventually Martynov was named by others.48 U.S. human intelligence operations in the Soviet Union, always a point of vulnerability, collapsed under the successful Soviet counterintelligence drive accelerated by Andropov—at least that is what Major General Rem Krasil’nikov, head of the first (American) department of the KGB’s Second Main Directorate (1979–1992), claims.

pages: 264 words: 79,589
Kingpin: How One Hacker Took Over the Billion-Dollar Cybercrime Underground by Kevin Poulsen
Apple II, Brian Krebs, Burning Man, corporate governance, dumpster diving, Exxon Valdez, fake news, gentrification, Hacker Ethic, hive mind, index card, Kickstarter, McMansion, Mercator projection, offshore financial centre, packet switching, pirate software, Ponzi scheme, Robert Hanssen: Double agent, Saturday Night Live, Silicon Valley, SQL injection, Steve Jobs, Steve Wozniak, Steven Levy, traffic fines, web application, WikiLeaks, zero day, Zipcar
Veteran FBI agents were dispatched from the Washington, DC, field office to investigate the attacks, and Mularski was one of fifteen fresh recruits sent to fill the vacancies in DC—the city marked thirty-second on his list. Almost overnight Mularski went from managing furniture stores to working on some of the FBI’s most important, and highly classified, investigations. When, in 1999, a listening device was found in an office on the top floor of the State Department’s headquarters, he was part of the team that identified a Russian diplomat monitoring the transmitter from outside. In 2001, he helped bring down Robert Hanssen, a fellow counterespionage agent who’d been secretly spying for the KGB and its successor agency for twenty years. It was heady work, but the secrecy chafed Mularski: He held a top-secret clearance and couldn’t talk about his job with outsiders—even his wife.
…
A couple of them looked like teenagers barely out of puberty; others were older, unkempt and vaguely dangerous in appearance. Around the table a handful of FBI agents in suits and ties stared back at the faces of the international computer underground. For one of the agents, a lot of things were suddenly making sense. At thirty-five years old, J. Keith Mularski had been an FBI agent for seven years. But he’d been on the computer crime beat for just four months, and he had a lot to learn. Enthusiastically friendly and quick to laugh, Mularski had wanted to be an FBI agent since his freshman year at Pennsylvania’s Westminster College, when a bureau recruiter came in to speak to one of his classes.
…
In 1997, after eight years of waiting, he finally decided he was ready for the FBI. After a yearlong application process and sixteen weeks of training at the FBI academy in Quantico, he was sworn in as an agent in July 1998. As part of the bureau’s graduation ritual, the newly minted agent was instructed to rank all the FBI field offices in order of assignment preference. He rated his hometown of Pittsburgh as number one—it was where Mularski had grown up, gone to school, and met his wife. His chances of transferring there evaporated the next month, when Islamic terrorists bombed U.S. embassy buildings in Kenya and Tanzania. Veteran FBI agents were dispatched from the Washington, DC, field office to investigate the attacks, and Mularski was one of fifteen fresh recruits sent to fill the vacancies in DC—the city marked thirty-second on his list.

Hiding in Plain Sight: The Invention of Donald Trump and the Erosion of America by Sarah Kendzior
4chan, Bear Stearns, Berlin Wall, Bernie Sanders, Black Lives Matter, borderless world, Brexit referendum, Cambridge Analytica, Carl Icahn, Chelsea Manning, Columbine, corporate raider, desegregation, disinformation, don't be evil, Donald Trump, drone strike, Edward Snowden, Evgeny Morozov, fake news, Ferguson, Missouri, Francis Fukuyama: the end of history, gentrification, Golden arches theory, hiring and firing, illegal immigration, income inequality, Jaron Lanier, Jeff Bezos, Jeffrey Epstein, Julian Assange, junk bonds, Michael Milken, military-industrial complex, Mohammed Bouazizi, Naomi Klein, Nelson Mandela, new economy, Oklahoma City bombing, opioid epidemic / opioid crisis, payday loans, plutocrats, public intellectual, QAnon, Robert Hanssen: Double agent, Ronald Reagan, side hustle, Silicon Valley, Skype, Steve Bannon, Thomas L Friedman, trickle-down economics, Twitter Arab Spring, unpaid internship, white flight, WikiLeaks, Y2K, zero-sum game
This is not to say that the Daily News was a paragon of journalistic integrity, but that the news still followed the old Mark Twain adage: “Get your facts straight first, and then you can distort them as much as you please.” We were not yet in a factual free-for-all: readers had the time to notice if we made mistakes, and we had the time to fix them. I did some reporting for the print side. My first article, in what now seems like ludicrous foreshadowing, was about Robert Hanssen—the FBI agent who was arrested in 2001 after spying for Russia for twenty-two years—writing pornographic stories on the internet, but my primary role was to keep the website operational. My small team was the least important part of the paper, until, one day, we weren’t. * * * I was out of town when the towers fell.
…
(Mueller investigated this branch of Chabad in 2017 but never revealed his findings.)31 Sater told the Los Angeles Times that he freelanced as an informant to the US government during the 2000s and spent the decade “building Trump Towers by day and hunting Bin Laden by night”32—an interesting claim given the rumored connection between al-Qaeda and the Russian mafia operation run by Sater family associate Mogilevich.33 Former KGB officer Aleksandr Litvinenko, who was murdered by Kremlin agents in 2006, claimed in 2005 that Mogilevich has had a good relationship with Russian president Vladimir Putin since 1994 or 1993 and that Mogilevich is in contact with al-Qaeda and sells them weapons. Given that Sater had worked as an FBI informant during the crucial years of 1998 to 2001, that the FBI had named Mogilevich their top priority in 2011, and that Sater had worked with the Trump family in a project that appears to have involved significant money-laundering, it is disconcerting at best that the FBI did not raise any concerns when Trump ran for office and won the nomination.
…
In 2019, a newly unsealed court document cites an Epstein accountant claiming that Robert Maxwell was the true source of Epstein’s fortune, but does not elaborate on how or when this happened.39 The full story of Mogilevich, the Maxwell family, and how they became connected to fellow sex trafficker Epstein remains a mystery—at least, to the public, due to the refusal of law enforcement officials to discuss it in detail. We know that Robert Maxwell was at the least an acquaintance of Trump in the late 1980s, part of the same corrupt circle of elites.40 They even bought their respective disastrous yachts from the same arms dealer, Adnan Khashoggi. After Epstein was arrested in July 2019, FBI agents raided his home and found that he had multiple passports, including an Austrian passport that listed his residence as Saudi Arabia.41 Later that month, reporter Vicky Ward revealed that when she had interviewed Alex Acosta shortly after Trump was elected, he told her, “I was told Epstein ‘belonged to intelligence’ and to leave it alone.”42 Acosta did not specify to which country’s intelligence Epstein belonged.

pages: 340 words: 91,745
Duped: Double Lives, False Identities, and the Con Man I Almost Married by Abby Ellin
Bernie Madoff, bitcoin, Burning Man, business intelligence, Charles Lindbergh, cognitive dissonance, cognitive load, content marketing, dark triade / dark tetrad, Donald Trump, double helix, dumpster diving, East Village, fake news, feminist movement, forensic accounting, fudge factor, hiring and firing, Internet Archive, John Darwin disappearance case, longitudinal study, Lyft, mandatory minimum, meta-analysis, pink-collar, Ponzi scheme, post-truth, Robert Hanssen: Double agent, Ronald Reagan, Silicon Valley, Skype, Snapchat, TED Talk, telemarketer, theory of mind, Thomas Kuhn: the structure of scientific revolutions
MI6 was bamboozled by Philby and the Cambridge Five, a ring of British spies who were really working for the KGB during World War II and beyond. (They were recruited while they were students at the University of Cambridge, which is where the name came from.) The FBI was deceived by Robert Hanssen, an FBI agent who was also in cahoots with the Russians, as was the CIA by Aldrich Ames, who was selling secrets to the KGB for millions of dollars in cash. The Agency was not happy. As former CIA agent Jack Devine told me, “We do that to others, not internally.”36 ANOTHER VERY INTELLIGENT person who was nonetheless swindled is Stephen Greenspan, an emeritus professor of educational psychology at the University of Connecticut.
…
“He told himself the story that his family would be better off without him, and that while his children did think he was dead, they were adults living their own lives, so it’s not as if he abandoned them as babies.”17 At a secret trial held at MI5 headquarters in Mayfair, London, in November 1952, eleven years before the truth finally came out, Kim Philby convinced his interrogator that he wasn’t a Soviet agent partly by stuttering whenever he was asked a question. Such skills bought him time to come up with another lie. He added that he was basically immune to detection, because he was born to the “governing class” and knew many people of great influence. “They’d never try to beat me up or knock me around, because if they had been proved wrong afterwards, I could have made a tremendous scandal,” he said.18 PHILBY WAS A natural deceiver. So is Bob Hamer.19 Hamer spent twenty-six years with the FBI, many of them as an undercover agent, successfully persuading bad people into believing he was one of them.
…
.), 202 false self, 69 families, 28 double lives and, 108, 122–123, 126–130, 175–176 lies and, 177–178 multiple, 65–66, 150 secrecy in, 35–36, 44–45 FBI, 40, 72, 151, 152 fugitives, 91–95, 102 undercover agents, 100–101 fear, cowardice and, 62 Feldman, Robert, 60 Fels, Anna, 123 Festinger, Leon, 147–148 The Final Nail (publication), 54 Fisher, Helen, 145–146 Fitness, Julie, 42 Five Factor model, 213–215 Folly of Fools (Trivers), 106–107 Fragments (Wilkomirski), 68 Franz, Volker, 205 fraud, 28, 29–30, 156 affinity, 151–152 with career credentials, 41 children as victims of identity, 172 gender, 134, 150 sexual assault by, 131–135 social media and, 41 Freeman, Rhonda, 125–126 Freshman, Audrey, 124 fugitives, FBI, 91–95, 102 “Fugitives Have More Fun: Confessions of a Wanted Eco-Terrorist” (speech), 55 Furnham, Adrian, 109 Gacy, John Wayne, 149–150 Galinsky, Adam, 205 galvanic skin response (GSR), 157, 201 gamesmanship, with psychopathy, 75 Gaslight (film), 33 gaslighting, 23, 25, 119, 129 gender, 176 fraud, 134, 150 honesty and, 172–175, 177–178 See also men; women Gere, Richard, 4 Get the Truth (Houston), 189 Gladwell, Malcolm, 31 Glass, Stephen, 150 Goldberg, Carrie, 135 Goodall, Jane, 83 Grafman, Jordan, 67, 151, 173–174, 216 Greeks, ancient, 86 Greene, Graham, 49, 152 Greenspan, Stephen, 151 Greenwood, Elizabeth, 99, 100 GSR.

pages: 282 words: 92,998
Cyber War: The Next Threat to National Security and What to Do About It by Richard A. Clarke, Robert Knake
air gap, barriers to entry, complexity theory, data acquisition, Dr. Strangelove, escalation ladder, Golden arches theory, Herman Kahn, information security, Just-in-time delivery, launch on warning, military-industrial complex, MITM: man-in-the-middle, nuclear winter, off-the-grid, packet switching, RAND corporation, Robert Hanssen: Double agent, Ronald Reagan, Seymour Hersh, Silicon Valley, smart grid, South China Sea, Steve Jobs, systems thinking, Timothy McVeigh, trade route, undersea cable, Y2K, zero day
If a Cold War spy wanted to move that much information out of a secret, classified facility, he would have needed a small moving van and a forklift. He also would have risked getting caught or killed. Robert Hanssen, the FBI employee who spied for the Soviets, and then the Russians, starting in the 1980s, never revealed anywhere near that much material in over two decades. He secreted documents out of FBI headquarters, wrapped them in plastic bags, and left them in dead drops in parks near his home in Virginia. In all, Hanssen’s betrayal amounted to no more than a few hundred pages of documents. Hanssen now spends twenty-three hours a day in solitary confinement in his cell at the supermax prison in Colorado Springs.
…
Beyond the exercise, there is good reason to believe that someone actually has already implanted logic bombs in the U.S. power grid control networks. Several people who should know implied or confirmed that the U.S. has also already engaged in the same kind of preparation of the battlefield. Imagine if the FBI announced that it had arrested dozens of Chinese government agents running around the country strapping C4 explosive charges to those big, ugly high-tension transmission line towers and to some of those unmanned step-down electric substation transformers that dot the landscape. The nation would be in an outrage. Certain Congressmen would demand that we declare war, or at least slap punitive tariffs on Chinese imports.
…
The Taiwanese hacker sitting in the San Francisco cyber café could still attack a Chinese government website. But under such an agreement the U.S. would have to stop the botnet and actively investigate the hacker. In the case of a hypothetical Taiwanese agent hacking into Chinese networks in violation of an international agreement, the U.S. government, when notified by China of such activity, would have to task the FBI or Secret Service to help the Chinese police track down the culprit in San Francisco. If he was found, he could be tried in a U.S. court for violation of U.S. law. Of course, nations may say that they are looking for hackers and not be.

The Billion Dollar Spy: A True Story of Cold War Espionage and Betrayal by David E. Hoffman
back-to-the-land, Berlin Wall, cuban missile crisis, disinformation, en.wikipedia.org, IFF: identification friend or foe, Mikhail Gorbachev, military-industrial complex, Robert Hanssen: Double agent, Ronald Reagan, Vladimir Vetrov: Farewell Dossier
According to a damage assessment by the CIA, nine of the agents whom Ames identified on June 13 were executed. The Senate Select Committee on Intelligence said Ames admitted compromising over a hundred U.S. intelligence operations of the CIA, FBI, military, and allied governments. The committee said “his betrayal stands as the most egregious in American history.” Still more damage was caused by Robert Hanssen, an FBI specialist on counterintelligence, who offered his services to the KGB in October 1985. Hanssen and Ames remained Soviet agents for years to come. On Ames, see Senate Select Committee on Intelligence, “Assessment of the Aldrich H. Ames Espionage Case and Its Implications for U.S.
…
Howard adamantly refused, saying he had been “screwed” by the polygraph in the past, reiterated that he was innocent, and again demanded time to consult a lawyer. The FBI then switched gears and said Howard would have to take a polygraph before seeing his lawyer. At that, Howard grew irate and said the FBI could do whatever it had to, including search his house. The FBI agents asked if he would sign a consent to be searched. Howard refused. The FBI agents said if he reconsidered, they would be around the next morning, and they gave him a phone number to call.9 The next day, a Friday, late in the day, Howard called the FBI agents in the hotel room, saying he had talked with a lawyer and suggested that, despite his fear of the polygraph test, he might agree to go through with it, to get the FBI “off his back” and to prove his innocence.
…
He then flew on to Helsinki.15 While Howard was jetting off, the FBI knocked on his front door in Santa Fe. It was 3:05 p.m. on Sunday. The special agents had just received word from Texas of an interview the FBI conducted there with Howard’s friend Bosch. The FBI agents felt that Bosch had corroborated the accusation that Howard gave information to the Soviets.16 The FBI special agents asked Mary where Howard was. Mary said he was out jogging and would return in half an hour.17 He never did. On Monday, a federal warrant was issued for the arrest of Edward Lee Howard on charges of espionage.18 But he had eluded the FBI, and they would never catch up.

pages: 443 words: 116,832
The Hacker and the State: Cyber Attacks and the New Normal of Geopolitics by Ben Buchanan
active measures, air gap, Bernie Sanders, bitcoin, blockchain, borderless world, Brian Krebs, British Empire, Cass Sunstein, citizen journalism, Citizen Lab, credit crunch, cryptocurrency, cuban missile crisis, data acquisition, disinformation, Donald Trump, drone strike, Edward Snowden, fake news, family office, Hacker News, hive mind, information security, Internet Archive, Jacob Appelbaum, John Markoff, John von Neumann, Julian Assange, Kevin Roose, Kickstarter, kremlinology, Laura Poitras, MITM: man-in-the-middle, Nate Silver, operational security, post-truth, profit motive, RAND corporation, ransomware, risk tolerance, Robert Hanssen: Double agent, rolodex, Ronald Reagan, Russian election interference, seminal paper, Silicon Valley, South China Sea, Steve Jobs, Stuxnet, subscription business, technoutopianism, undersea cable, uranium enrichment, Vladimir Vetrov: Farewell Dossier, Wargames Reagan, WikiLeaks, zero day
For more on how news of the missiles’ presence was dismissed by agency senior leaders, see Sean D. Naylor, “Operation Cobra: The Untold Story of How a CIA Officer Trained a Network of Agents Who Found the Soviet Missiles in Cuba,” Yahoo News, January 23, 2019. 12. Gus W. Weiss, “The Farewell Dossier: Duping the Soviets,” CIA: Studies in Intelligence 39, no. 5 (1996). Deception certainly cut the other way, too. It was not until after the Cold War ended that the United States realized that two members of its intelligence community, Robert Hanssen and Aldrich Ames, had independently sold reams of classified information to the Soviets, including information on which Soviet officers were American spies. 13.
…
At some point in 2015, the American government became aware of the intrusion at the DNC and alerted the committee’s network administrators. In September 2015, an agent from the FBI called the main phone line at the DNC with the news. The person who answered transferred him to the IT help desk, where his call was eventually addressed. Afterward, an internal DNC memo passed along the news: “The F.B.I. thinks the D.N.C. has at least one compromised computer on its network and the F.B.I. wanted to know if the D.N.C. is aware, and if so, what the D.N.C. is doing about it.” The FBI agent had also specifically linked the intrusion to “the Dukes,” a common name in the cybersecurity community for the well-known group of hackers.
…
As a result, and in part due to the fact that the FBI agent had not provided proof of his identity, he did not return subsequent follow-up phone calls from the bureau. Despite the ongoing silence from the DNC, the FBI did not call any high-ranking officials there, nor did it show up in person to press the case at the offices, which were located just a mile away from the FBI field office. The bureau chose not to send follow-up emails, likely due to the strong possibility that the Russians were capable of accessing the DNC’s mail servers. The investigation stalled. The hackers remained in place. In November, the FBI called again. This time, agents issued a more strident warning.

pages: 556 words: 141,069
The Profiteers by Sally Denton
Albert Einstein, anti-communist, Ayatollah Khomeini, Bay Area Rapid Transit, Berlin Wall, Boycotts of Israel, clean water, company town, corporate governance, crony capitalism, disinformation, Donald Trump, Edward Snowden, energy security, Fall of the Berlin Wall, G4S, invisible hand, James Watt: steam engine, Joan Didion, Kitchen Debate, laissez-faire capitalism, Lewis Mumford, megaproject, Mikhail Gorbachev, military-industrial complex, mutually assured destruction, Naomi Klein, new economy, nuclear winter, power law, profit motive, Robert Hanssen: Double agent, Ronald Reagan, Seymour Hersh, Silicon Valley, trickle-down economics, uranium enrichment, urban planning, vertical integration, WikiLeaks, wikimedia commons, William Langewiesche
“contradicted what the US government”: Phelan, “True Motives Behind Sentencing of Jonathan Pollard.” “Year of the Spy”: The CIA dubbed 1985 the Year of the Spy because fourteen Americans were arrested and/or convicted of spying for the Soviet Union and its allies, as well as for Israel, China, and Ghana. Included were John Walker, Edward Lee Howard, Aldrich Ames, and Robert Hanssen. “busted the most secret” . . . “Neither Pollard nor the government”: Loftus and Aarons, Secret War, 402. Loftus and Aarons contend that by fixing the beginning date for Iran-Contra in 1985 rather than in 1984, as Pollard contended, the Reagan administration attempted to scapegoat Israel. “In its rush to conclude the Iran-Contra inquiry in just three months, Congress ignored several leads to the 1984 French connection and started its investigation with the Israeli involvement in 1985.
…
.”: Wesley Phelan, “The True Motives Behind the Sentencing of Jonathan Pollard” (interview with Angelo Codevilla), Washington Weekly, January 11, 1999. “were of a number”: Crovitz, “Even Pollard Deserves.” Lohbeck would contend that he never purchased any classified documents from Pollard, but rather was used by Pollard as a “red herring to throw [FBI agents] off the trail of the Israeli agent” who had bought the documents. Pollard identified Lohbeck as “a recognized liaison to the [Afghan] mujahideen” who had access to classified documents. Also see Erwin Knoll, “Journalistic Jihad: Holes in the Coverage of a Holy War,” Progressive, May 1990, 17–22. “Jay laughed”: Lohbeck, 133.
…
“triangular relationship”: Gusterson, “Assault on Los Alamos.” “plowing much”: Gusterson, “Assault on Los Alamos.” “the Margaret Mead of the weapons labs”: Ibid. “China Stole”: James Risen and Jeff Gerth, “China Stole Nuclear Secrets for Bombs, US Aides Say,” New York Times, March 6, 1999. “hoping for a glimpse” . . . “Convoys of FBI” . . . “FBI agents descended”: Gusterson, “Assault on Los Alamos.” “Reporters and congressmen”: Stober and Hoffman, Convenient Spy, 209. “I am truly sorry” . . . “As a member”: James Parker, quoted in Wen Ho Lee, My Country Versus Me: The First-Hand Account by the Los Alamos Scientist Who Was Falsely Accused of Being a Spy (New York: Hachette, 2002), 2.

The Secret World: A History of Intelligence by Christopher Andrew
Able Archer 83, active measures, Admiral Zheng, airport security, anti-communist, Atahualpa, Ayatollah Khomeini, Bletchley Park, British Empire, Chelsea Manning, classic study, colonial rule, cuban missile crisis, disinformation, Edward Snowden, en.wikipedia.org, Etonian, Fellow of the Royal Society, Francisco Pizarro, Google Earth, information security, invention of movable type, invention of the telegraph, Julian Assange, Khyber Pass, Mahatma Gandhi, Mikhail Gorbachev, Murano, Venice glass, RAND corporation, Robert Hanssen: Double agent, Ronald Reagan, Skype, South Sea Bubble, spice trade, Suez canal 1869, Suez crisis 1956, the market place, trade route, two and twenty, union organizing, uranium enrichment, Vladimir Vetrov: Farewell Dossier, WikiLeaks, éminence grise
FBI and CIA investigators expected to hear the voice of Brian Kelley. Instead, they heard Robert Hanssen. When arrested on 18 February 2001, Hanssen asked the FBI agents: ‘What took you so long?’53‡ In July he was sentenced to life imprisonment without the possibility of parole. So far as counter-intelligence was concerned, the Ames, Nicholson and Hanssen cases, together with the incompetent handling of the Kelley investigation, collectively demolish the claim of the Aspin–Brown Commission in its 1996 report that the United States had ‘without question . . . the most capable intelligence apparatus of any country in the world’. Despite its general belief in the global superiority of US intelligence, however, the Commission did briefly acknowledge that the relationship between intelligence agencies and policymakers in Washington worked less well than in several US allies: Intelligence must be closer to those it serves.
…
May, ‘An Identity of Opinion: Historians and July 1914’, Journal of Modern History, vol. 79 (2007), no. 2 Wills, Garry, Bomb Power: The Modern Presidency and the National Security State (New York: Penguin, 2010) Wilson, Frances, ‘The Lost Art of Table Talk’, Literary Review, February 2014 Wise, David, Spy: The Inside Story of How the FBI’s Robert Hanssen Betrayed America (New York: Random House, 2003) Witte, S., The Memoirs of Count Witte (New York: Doubleday, 1921) Wolf, Markus (with Anne McElvoy), Man without a Face: The Autobiography of Communism’s Greatest Spymaster (London: Jonathan Cape, 1997) Wood, Michael, Conquistadors (London: BBC Books, 2000) Woodham-Smith, Cecil, The Reason Why: Story of the Fatal Charge of the Light Brigade (London: Constable, 1953) Woods, Kevin, James Lacey and Williamson Murray, ‘Saddam’s Delusions: The View from the Inside’, Foreign Affairs, vol. 85 (2006), no. 3 Woodward, David, The American Army and the First World War (Cambridge: Cambridge University Press, 2014) Worcester, Edward Somerset, Marquess of, Three letters intercepted by Sir Tho: Fairfax in Cornwal.
…
On one occasion the investigators sent a bogus SVR officer to his front door to warn him that, because of the FBI’s evidence against him, it was essential for him to escape: ‘Meet us tomorrow night at the [Washington] Vienna Metro. A person will approach you. We have a passport for you, and we’ll get you out of the country.’ Kelley slammed the door and reported the incident to the FBI. He was eventually vindicated as the result of a file exfiltrated from SVR archives in 2000 in an operation which cost the FBI seven million dollars. The file contained tape of the US agent speaking to his Russian case officer. FBI and CIA investigators expected to hear the voice of Brian Kelley.

pages: 719 words: 209,224
The Dead Hand: The Untold Story of the Cold War Arms Race and Its Dangerous Legacy by David Hoffman
Able Archer 83, active measures, anti-communist, banking crisis, Berlin Wall, Boeing 747, Chuck Templeton: OpenTable:, crony capitalism, cuban missile crisis, disinformation, failed state, guns versus butter model, It's morning again in America, joint-stock company, Kickstarter, Korean Air Lines Flight 007, launch on warning, Mikhail Gorbachev, military-industrial complex, mutually assured destruction, nuclear winter, Oklahoma City bombing, radical decentralization, Robert Hanssen: Double agent, rolodex, Ronald Reagan, Ronald Reagan: Tear down this wall, Seymour Hersh, Silicon Valley, standardized shipping container, Stanislav Petrov, Strategic Defense Initiative, Thomas L Friedman, undersea cable, uranium enrichment, Vladimir Vetrov: Farewell Dossier, warehouse robotics, zero-sum game
"Casey was like a child with a new toy with Yurchenko," Gates said. "Not only was he eager to hear, virtually on a daily basis, about the debriefings: he also could not help bragging about this great CIA coup. He met with Yurchenko, had dinner with him, couldn't get enough of him."26 On October 1, 1985, Robert Hanssen, an FBI analyst on Soviet intelligence, dropped a letter into a mailbox in Prince George's County, outside of Washington. Hanssen was based in the New York office but was working that day in the capital. The letter was addressed to the home of a KGB operative, Viktor Degtyar, who lived in Alexandria, Virginia.
…
Walker's partners in espionage included Jerry Whitworth, who had served on the U.S.S. Enterprise and leaked classified communications from the Pacific Ocean exercises in 1983. Walker did not realize it on this night, but the FBI, after months of investigation, was closing in on him and watching his every move in the woods. When Walker drove away, an FBI agent picked up the 7-Up can, intended as a signal to the Soviets that Walker had left them something and wanted to pick up money. Then the FBI found the brown paper bag, and in the bottom of it was an inch-thick package, wrapped in a white plastic garbage sack. The corners were neatly folded over and taped.
…
At the elevator, Walker was arrested by the FBI. Soon, U.S. intelligence and military officials began to unravel the incredible story of how Walker had given away some of the deepest secrets of the Cold War. On May 28, in Moscow, Gordievsky took some pep pills the British had given him in London to fight fatigue. At the office, he was summoned to meet agents from KGB counterintelligence who wanted to talk about possible penetration of the KGB in London. Gordievsky was driven several miles from headquarters to a small bungalow, where he met the agents. They had lunch, and a servant poured them all a brandy.

pages: 826 words: 231,966
GCHQ by Richard Aldrich
belly landing, Berlin Wall, Bletchley Park, British Empire, Charles Babbage, colonial exploitation, cuban missile crisis, disinformation, friendly fire, illegal immigration, index card, it's over 9,000, lateral thinking, machine translation, Menlo Park, Mikhail Gorbachev, Neil Kinnock, New Journalism, operational security, packet switching, private military company, Robert Hanssen: Double agent, Ronald Reagan, Seymour Hersh, social intelligence, South China Sea, Suez crisis 1956, undersea cable, unit 8200, University of East Anglia, Yom Kippur War, Zimmermann PGP
To cap it all, in November 1985 it was discovered that Jonathan Pollard, a Mossad spy inside the Pentagon, had been handing over very sensitive material to the Israelis. The Americans had not yet uncovered the two best covert sources employed by the Soviets, namely a CIA officer called Aldrich Ames and an FBI officer, Robert Hanssen.22 These frightening cases of KGB espionage had a direct impact on the British, since they made Bill Odom all the keener to see the polygraph deployed by GCHQ at Cheltenham.23 Alongside KGB espionage, the other big issue of the time was relations between the Western sigint allies. In 1985 the United States cut off the intelligence flow to New Zealand, one of the ‘second party’ members of UKUSA.
…
They contained worrying news: For one year, a large amount of very valuable documentary material concerning the work of the Americans on deciphering Soviet cyphers, intercepting and analysing open-radio correspondence of Soviet Institutions was received…On the basis of Weisband material, our state security organs carried out a number of defensive measures, resulting in the reduced efficiency of the American deciphering service. This has led to a considerable current reduction in the amount of deciphering and analysis by the Americans.29 In May 1950 Weisband was named by another agent who had been revealed by Venona and interrogated by the FBI. Although Weisband was questioned, there was insufficient evidence to charge him. There was also a fear that a court case would advertise the work of signals intelligence to other countries, which might then take steps to upgrade their communications. He was never prosecuted for espionage.30 Yet Weisband caused immense damage to Western code-breaking.
…
., The First Directorate: My First 32 Years in Intelligence and Espionage Against the West – The Ultimate Memoirs of a Master Spy (NY: St Martin’s Press, 1994) King, C.H., The Cecil King Diaries, 1965–1970 (Jonathan Cape, 1972) Kot, S., Conversations with the Kremlin and Dispatches from Russia (Oxford: Oxford UP, 1963) Lamphere, R.J. and Shachtman, T., The FBI-KGB War: A Special Agent’s Story (W.H. Allen, 1986) Lawson, N., The View From No.11: Memoirs of a Tory Radical (Heinemann, 1992) Lederer, W., The Last Cruise: The Sinking of the Submarine USS Cochino (William Sloane, 1950) Leutze, J. (ed.), The London Observer: The Journal of General Raymond E. Lee, 1940–1941 (Hutchinson, 1972) McGehee, R.W., Deadly Deceits: My 25 Years in the CIA (NY: Sheridan Square, 1983) McManners, H., Falklands Commando (William Kimber, 1984) —Forgotten Voices of the Falklands: The Real Story of the Falklands War (Ebury, 2008) Machon, A., Spies, Lies and Whistleblowers: MI5, MI6 and the Shayler Affair (Lewes: The Book Guild, 2005) Major, J., The Autobiography (HarperCollins, 1999) Mathams, R.H., Sub-Rosa; Memoirs of an Australian Intelligence Analyst (Sydney: Allen and Unwin, 1982) Mendez, A. and J., Spy Dust: Two Masters of Disguise Reveal the Tools and Operations that Helped Win the Cold War (NY: Atria Books, 2002) Mills, D., My Life as a Coder (Special), D/MX 919781, 1952–54 (Branston, Lincs: privately published, 2005) Modin, Y., My Five Cambridge Friends (Headline, 1994) Nott, J., Here Today Gone Tomorrow: Recollections of an Errant Politician (Politico’s, 2002) Owen, D., Time to Declare (Michael Joseph, 1991) Patten, C., Not Quite the Diplomat: Home Truths About World Affairs (Allen Lane, 2005) Pavlov, V., Memoirs of a Spymaster: My Fifty Years in the KGB (NY: Carroll and Graf, 1994) Philby, K., My Silent War (MacGibbon and Key, 1968) Prime, R., Time of Trial: The Personal Story Behind the Cheltenham Spy Scandal (Hodder and Stoughton, 1984) Prior, J., A Balance of Power (Hamish Hamilton, 1986) Putney, D.

pages: 889 words: 433,897
The Best of 2600: A Hacker Odyssey by Emmanuel Goldstein
affirmative action, Apple II, benefit corporation, call centre, disinformation, don't be evil, Firefox, game design, Hacker Ethic, hiring and firing, information retrieval, information security, John Markoff, John Perry Barlow, late fees, license plate recognition, Mitch Kapor, MITM: man-in-the-middle, Oklahoma City bombing, optical character recognition, OSI model, packet switching, pirate software, place-making, profit motive, QWERTY keyboard, RFID, Robert Hanssen: Double agent, rolodex, Ronald Reagan, satellite internet, Silicon Valley, Skype, spectrum auction, statistical model, Steve Jobs, Steve Wozniak, Steven Levy, Telecommunications Act of 1996, telemarketer, undersea cable, UUNET, Y2K
Surveillance societies have appeared in the not so recent past, and they were frightening indeed. Stalin’s Russia. Ceausescu’s Romania. Hoenecker’s East Germany. Perhaps the United States can avoid the mistakes made by the surveillance societies of the twentieth century. And perhaps J. Edgar Hoover’s FBI is also completely honest, professional, and incorruptible— just like Robert Hanssen. Vonage Broadband Security Risk (Spring, 2004) By Kevin T. Blakley As a 15-year security professional and Vonage phone-service user over the past six months, I have uncovered some serious security problems with its use and solutions to possible security risks for both business and home users.
…
The term “pirate” rather than “phreak” is used here because the vast majority of illegitimate CMT users (Cellular Mobile Telephone) are only interested in stealing airtime, while phone phreaks are mainly interested in learning more about the telephone network through its manipulation. The six-month FBI investigation used “cooperative sources” who named fraudulent installers; then FBI agents posing as customers and installers used standard entrapment techniques to gather evidence against those allegedly involved. The FBI’s press release statement that “recent technological advances in computerized telephone switching equipment and billing systems were instrumental in....(their investigation)” is deliberately misleading. New York cellular carrier NYNEX merely supplied the FBI with its billing data to document the use of bogus and stolen ESN’s & MIN’s (Electronic Serial Numbers and Mobile Identification Numbers) discovered in the investigation.
…
The sheer overwhelming difficulty of this task may kill this investigation, especially as they find that many hackers simply leave false information. Computer hobbyists all across the country have already been called by the Bound Brook, New Jersey office of the FBI. They reported that the FBI agents used scare tactics in order to force confessions or to provoke them into turning in others. We would like to remind those who get called that there is nothing inherently wrong or illegal in calling any BBS, nor in talking about any activity. The FBI would not comment on the case as it is an “ongoing investigation” and in the hands of the local prosecutor. They will soon find that many on the Private Sector BBS’s user list are data processing managers, telecommunications security people, and others who are interested in the subject matter of the BBS, hardly the underground community of computer criminals depicted at the news conference.

pages: 1,744 words: 458,385
The Defence of the Realm by Christopher Andrew
Able Archer 83, active measures, anti-communist, Ayatollah Khomeini, Berlin Wall, Bletchley Park, Boeing 747, British Empire, classic study, Clive Stafford Smith, collective bargaining, credit crunch, cuban missile crisis, Desert Island Discs, disinformation, Etonian, Fall of the Berlin Wall, false flag, G4S, glass ceiling, illegal immigration, information security, job satisfaction, large denomination, liquidationism / Banker’s doctrine / the Treasury view, Mahatma Gandhi, Mikhail Gorbachev, Neil Kinnock, North Sea oil, operational security, post-work, Red Clydeside, Robert Hanssen: Double agent, Ronald Reagan, sexual politics, strikebreaker, Suez crisis 1956, Torches of Freedom, traveling salesman, union organizing, uranium enrichment, Vladimir Vetrov: Farewell Dossier, Winter of Discontent, work culture
Three Soviet agents (who, interestingly, included George Blake) were regarded as having ‘other’ motives. A majority of the most important cases, however, were ideological.38 The Service’s categorization of motives was arguably less satisfactory than the FBI MICE acronym (money, ideology, compromise, ego); ego, omitted in the Security Service analysis, has frequently been an important subsidiary motive in cases ranging from the Cambridge Five to the Americans Aldrich Ames and Robert Hanssen. In sixteen of the forty-three cases the main initial lead to detection had come from Service sources, eleven from defectors, eight from liaison and eight from other sources.39 By far the most serious counter-espionage case for the Security Service in the final decade of the Cold War began on Easter Sunday 1983 when Michael Bettaney, a heavy-drinking, disaffected officer in K4 (the department responsible for the investigation and analysis of Soviet London residencies), pushed through the letter-box in Holland Park of Arkadi Guk, the KGB resident, an envelope containing the case put by the Security Service for expelling three Soviet intelligence officers in the previous month, together with details of how all three had been detected.
…
On the morning of 12 July 1989 he looked out of his office window, saw two men tampering with his car and rushed downstairs to confront them. The men turned out to be FBI agents examining the car.64 A possibly over-dramatized account of what happened next was relayed to Head Office by SLO Washington. The FBI officer supervising the agents was reported to have been told by his field office: ‘Either you arrest the two FBI agents interfering with the car or you arrest Johnson.’ Having decided, without much difficulty, on the second option, the FBI officer was said to have informed Johnson, ‘Only in America do you interrupt two men breaking into your car and find that you are the one who is arrested!’
…
CROWN was identified as Guenther Rumrich, a twenty-sevenyear-old US army deserter, who was convicted with several of his accomplices in an Abwehr spy-ring at a highly publicized trial.135 As a result of US inter-agency confusion, others who had been indicted succeeded in escaping. J. Edgar Hoover, the FBI Director, and the prosecuting attorney blamed each other. The judge, to Hoover’s fury, blamed the FBI. Leon G. Turrou, the FBI special agent in charge of Rumrich’s interrogation, was so poorly briefed that he confused the Abwehr with the Gestapo.136 Though the Security Service was far better informed than the FBI, there were large gaps in its understanding of the organization of pre-war German intelligence.137 Possibly the largest was its lack of awareness of the Etappe Dienst naval network, eventually discovered as a result of German records captured in 1945.